According to Bitkom Research, 84% of companies surveyed in the critical infrastructure sectors expect an increase in cyberattacks in the next 12 months.
The requirements for critical infrastructure operators are increasing accordingly. Section 2 “Energy” of the BSI-KRITIS-Regulation, for example, mandates the establishment and certification of an information security management system. ISO 27001 27001 contains protection goals and states that cryptography and firewalls should be used. In addition, IEC 62443 specifies the requirements for controlling physical systems. Section 8 “Transport and Traffic” regulates the requirements for public transport, trans-European network corridors and the IP network related to rail operation.
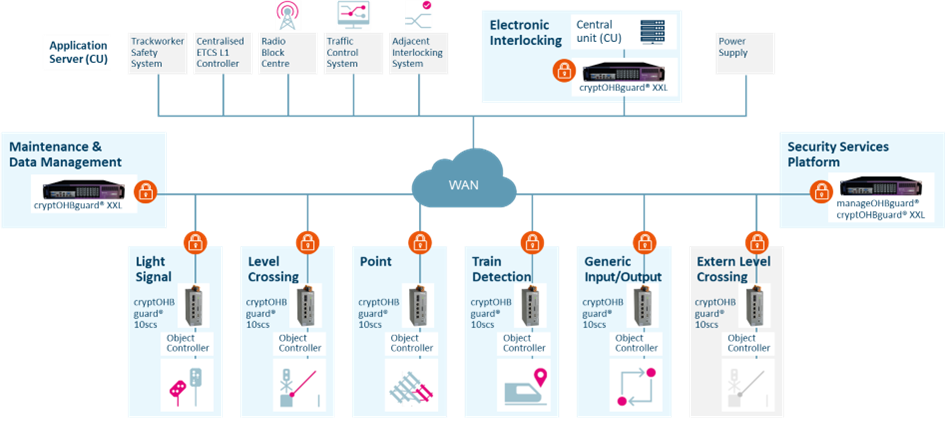
With the successful market launch of our new product cryptOHBguard® into the product range of the cyberOHBguard series, we can cover all of the aforementioned matters and requirements. This enables widely networked, secure digitalisation projects to be implemented under demanding environmental conditions.
FIELDS OF APPLICATION
Wherever you need a large number of decentralised cybersecurity components to be deployed in a “harsh” environment, cyberOHBguard series products are the preferred choice. In addition to their application in rail networks, our solutions are also suitable for the following industries and fields of application:
- Digitalisation of energy transfer or transport networks::
Secure data connections as a basis for the smart control of complex network infrastructures and more efficient load and feed-in management. - Digitalisation of motorway/transportation infrastructure::
Secure data encryption and transmission for autonomous driving and intelligent traffic routing with minimal latency, even under extreme temperature conditions - Digitalisation of waterway infrastructure:
Solutions for automated and networked inland waterway transport as a basis for increased utilisation of waterways and as a result environment-friendly goods transport
RAILWAY CONTROL BY EULYNX
Kosteneffiziente Modernisierung durch modulare Struktur
Thanks to its modular structure and EULYNX compatibility, rail operators can cost-effectively adapt and modernize their infrastructure. The open system architecture enables easy integration of new technologies without dependence on specific manufacturers.
Future-proof rail infrastructure with OHB
With the gridOHBguard series, we combine efficient data acquisition, flexible integration, and maximum security to offer railway operators a powerful and future-proof solution for monitoring and optimizing their infrastructure. With support for the EULYNX standard and cyberOHBguard security solutions, the efficiency, security, and flexibility of railway systems are taken to a new level.
The separation of infrastructure from the actual signal box technology is a key feature of modern architectures.
Highly available power supply, state-of-the-art fiber-optic technology, and secure data transmission form the backbone of the architecture.
Centralized and decentralized safety components that communicate via Ethernet using safety protocols provide safety with a high SIL level.
A key advantage of this architecture is that large-scale systems can be built independently of one another. This potentially offers the possibility of accelerating expansion.
Our cryptOHBguard® is included in the CC certifications and approvals issued by the BSI alongside genuscreen, which significantly enhances baseline protection.
The cryptOHBguard® 10scs is the top choice for field-level deployment in harsh environments.
BSI Certification:
Certification Report BSI-DSZ-CC-1194-2023-MA-01
Certification Report BSI-DSZ-CC-1194-2023
Security Target BSI-DSZ-CC-1194-2023-MA-01
Security Target BSI-DSZ-CC-1194-2023
For use in central data center environments, we offer the cryptOHBguard® S-XXL.
With the manageOHBguard®, more than 10,000 components can be managed centrally in a single tool. It is used to trigger alerts in the event of system anomalies. If necessary, parts of the network or individual components can be automatically shut down.
The monitorOHBguard® is used to monitor all network and OT security components within the system.
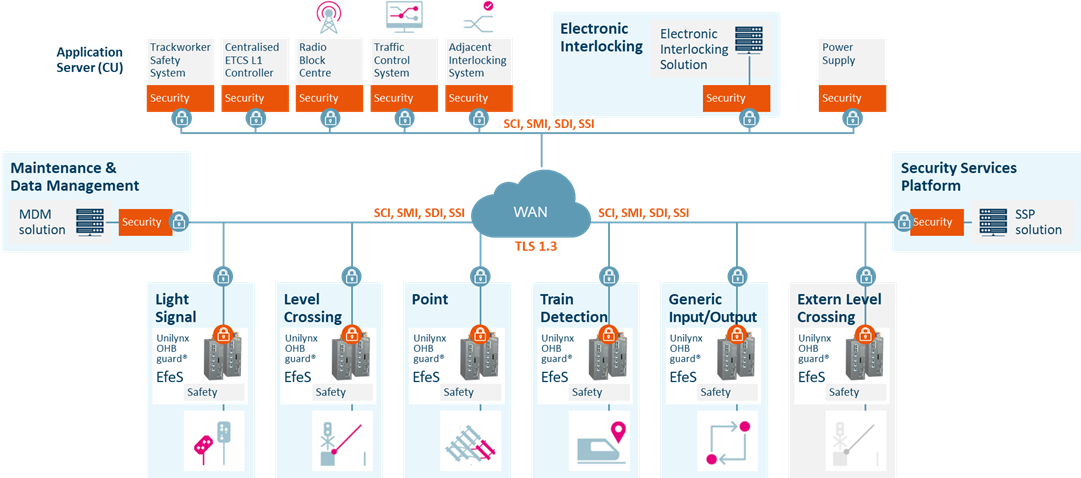
EULYNX SECURITY VARIANT B WITH THE NEW UNILYNXOHBGUARD®
The unilynxOHBguard® is a versatile connectivity manager for all EULYNX-compliant railway applications, offering various connection options and secure communication based on the EULYNX and System Pillar standards. It enables open network communication in accordance with CENELEC Cat. 3 standards and ensures secure, non-interfering data transmission from OT to IT networks.
BENEFITS AT A GLANCE
-
Extensive options for secure communication
- Standardized EULYNX interfaces: SSI, SDI, SMI
- OPC UA aggregator
- Simple and flexible configuration
- Local SMI as an alternative to the MDM server
UNILYNXOHBGUARD® ONE-STOP SECURITY SOLUTION
The unilynxOHBguard® ensures secure and reliable communication between EFES object controllers and signal processing systems. It manages the secure transmission of commands and messages (SCI), diagnostic and maintenance data (SDI & SMI), and safety services (SSI) for EULYNX subsystems. It offers several security options, including TLS over TCP for RaSTA and OPC UA communication, as well as tunneling for connections between two or more EFES. Thanks to its simple and flexible configuration, it can act as a connection manager for all Eulynx Fieldelement Subsystems (EFES) and efficiently manage multiple RaSTA connections.
FUTURE-PROOF STANDARDIZATION: EULYNX PROTOCOLS
unilynxOHBguard® uses interfaces developed in accordance with the EULYNX Baseline 4 standard, ensuring seamless communication with signal box systems, maintenance and data management (MDM) servers, and safety platforms. The system supports communication over Cat. 3 networks, providing a secure and robust framework for connectivity.
Adherence to standardized interfaces prevents lock-in to a specific technology and promotes flexibility and compatibility. By supporting EULYNX specifications, the unilynxOHBguard® optimizes the integration of signaling, point control, level crossing control, and train detection systems, and streamlines railway operations.
- SCI Standard Communication Interface
- SSI Standard Safety Interface
- SDI Standard Diagnostic Interface
- SMI Standard Maintenance Interface
The unilynxOHBguard® is a dedicated connectivity manager for all Eulynx Field Element Subsystems (EFES). It is responsible for establishing secure communication with external systems over open networks.
UNCOMPROMISING CYBER SECURITY
Ensuring safety and security is of critical importance in railway operations: the unilynxOHBguard® supports Category 3 networks and integrates advanced cybersecurity measures to protect data. The use of Ethernet-based communication reduces the need for extensive cabling. This lowers installation and maintenance costs and streamlines the entire installation process. The necessary infrastructure is integrated via the Security Service Interface (EULYNX SSI-XX), which provides all the functions required for secure data transmission (TLS over TCP).
OPC UA Communication for Diagnostics and Maintenance
In accordance with EULYNX, the OPC UA protocol is used to enable the transmission of diagnostic data to the Maintenance and Data Management (MDM) servers. Application-specific communication is structured according to the Standardized Diagnostic Interface (SDI) data model, ensuring a systematic and efficient exchange of information.
In addition, the OPC UA standard is used to enable the transfer of maintenance data—such as updates, patches, or new configuration files—from an MDM server to the Object Controller. If no MDM server is available, local MDM software can perform this task.
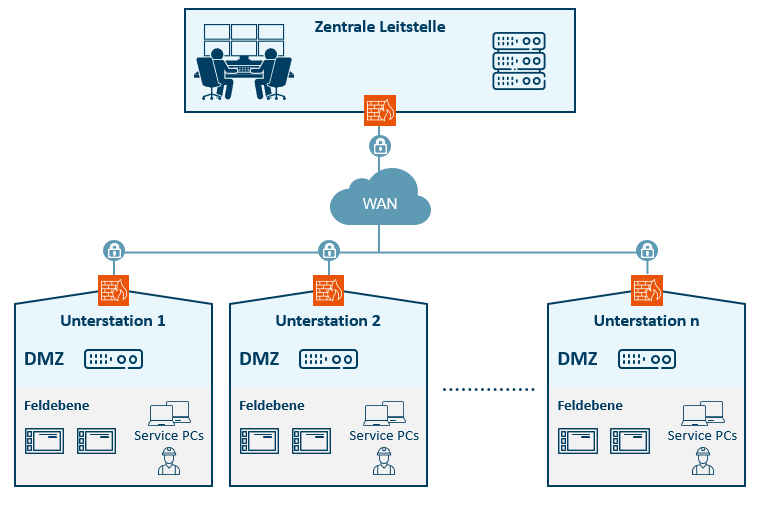
DMZ as protection against unauthorized access to security-relevant systems
A demilitarized zone (DMZ) is a computer network with security-controlled access to the servers connected to it.
The systems in the DMZ are shielded from other networks by firewalls. This separation allows access to publicly accessible services and at the same time protects the internal network from unauthorized access from outside. The purpose is to make services of the computer network available to both the WAN and the LAN on a secure basis.
A DMZ provides protection by isolating a system from two or more networks.
Our DMZ solution consists of a firewall and an industrial PC as the hardware basis, on which all applications relevant to the application are implemented as virtual machines.